It essentially asks: “how are consumers adapting, modifying and transforming my proprietary products and how can it be useful to my company’s innovation process in the future?”. Occurring between design production and design consumption, it provides a source of further innovation and wider business opportunities as well as highlighting unmet needs, vital to inform internal design trajectories.
It is an important topic because more and more products are becoming digitised, modularised and interconnected resulting in more opportunities for consumers to reprogram, adapt, modify and transform intellectual property as they locally see fit. The challenge for firms becomes one of how to identify, understand, capture and internalise external forms of generatively and innovation back inside firm boundaries to develop internal design competencies and capabilities. Firms who ignore or are unaware of their hacker innovator activities may lose-out to competitors who are able to find ways to engage, nurture and exploit through harnessing vital innovative ideas, features, functionalities to help drive continued growth.
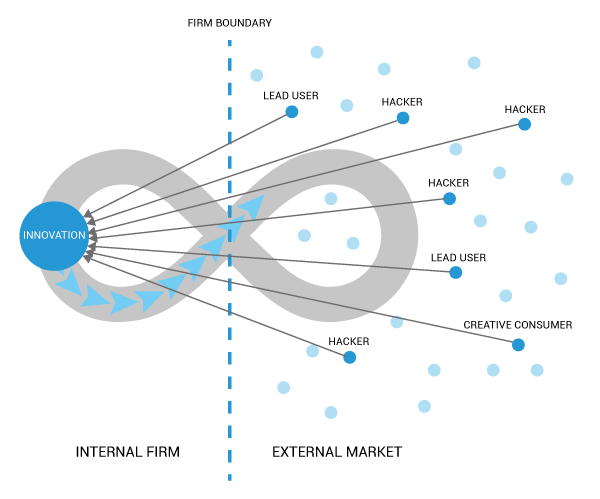
Design managers and strategists can respond in one of several ways to hacker innovation: discourage, resist, encourage or enable. My interest relates to the enable option by capturing and creating further value from hacker innovation. Here firms are overtly active in facilitating and exploiting creative activities as a vital source of future innovation. Firms must firstly be aware of external hacker innovation activities, analyse the impact on the wider business and innovation strategy and finally, formulate a suitable and appropriate response. In the case of enabling hacker innovation, appropriate distributed digital systems are essential to host, track, control and absorb external hacker innovation activities back into the firm to evaluate and use for further value creation and product development.
In recent research study carried-out within the smartphone industry on XDA Developer’s device hacking community (consisting over 7 million members), it has been estimated that a mere ~0.1% consumers hack their devices. Despite the low proportion in relation to overall consumers, there is empirical evidence of firms actively absorbing and implementing community ideas, features and innovation through passive backdoor channels to internal R&D teams as a complementary innovation source in future product software releases. If you would like to read more about this, you can download latest research paper: External hacker communities and industry-wide innovation sources: The role of autonomous end-users and consumers on internal R&D teams within device manufacturing firms.